In an era of cloud computing, AI-driven applications, and real-time data processing, databases sit at the core of nearly every business system. Yet despite growing cyber threats and stricter regulations, database security remains one of the most overlooked areas of enterprise security. In 2026, many organizations continue to invest heavily in perimeter defenses while leaving their most valuable asset—data—insufficiently protected.
This article examines why database security is still a blind spot for many companies and what risks this oversight creates in modern IT environments. Fast Tract IT Services – FZCO supports enterprises in strengthening database security frameworks, implementing robust access controls, encryption strategies, and continuous monitoring solutions to safeguard critical data assets in today’s complex digital landscape.
Databases Hold the Most Valuable Targets
Sensitive Data Concentrated in One Place
Databases store the information attackers want most: customer records, financial data, intellectual property, credentials, and operational data. A single database breach can expose millions of records and cause long-term reputational damage.
Despite this, database security is often assumed to be “handled” by default configurations or inherited from infrastructure-level controls, which is rarely enough.
Attackers Target Data, Not Just Systems
Modern cyberattacks are increasingly data-focused. Instead of disrupting systems, attackers aim to quietly access, exfiltrate, or manipulate data over time. Weak database security gives them exactly the access they need, especially in environments exposed to evolving cloud database security threats.

Why Database Security Gets Overlooked
Overreliance on Network and Cloud Security
Many companies believe that firewalls, VPNs, and cloud provider security are sufficient. While these controls are important, they do not protect against:
- Compromised credentials
- Insider threats
- Misconfigured database access
- Application-level vulnerabilities
Database security requires dedicated controls at the data layer, not just at the perimeter.
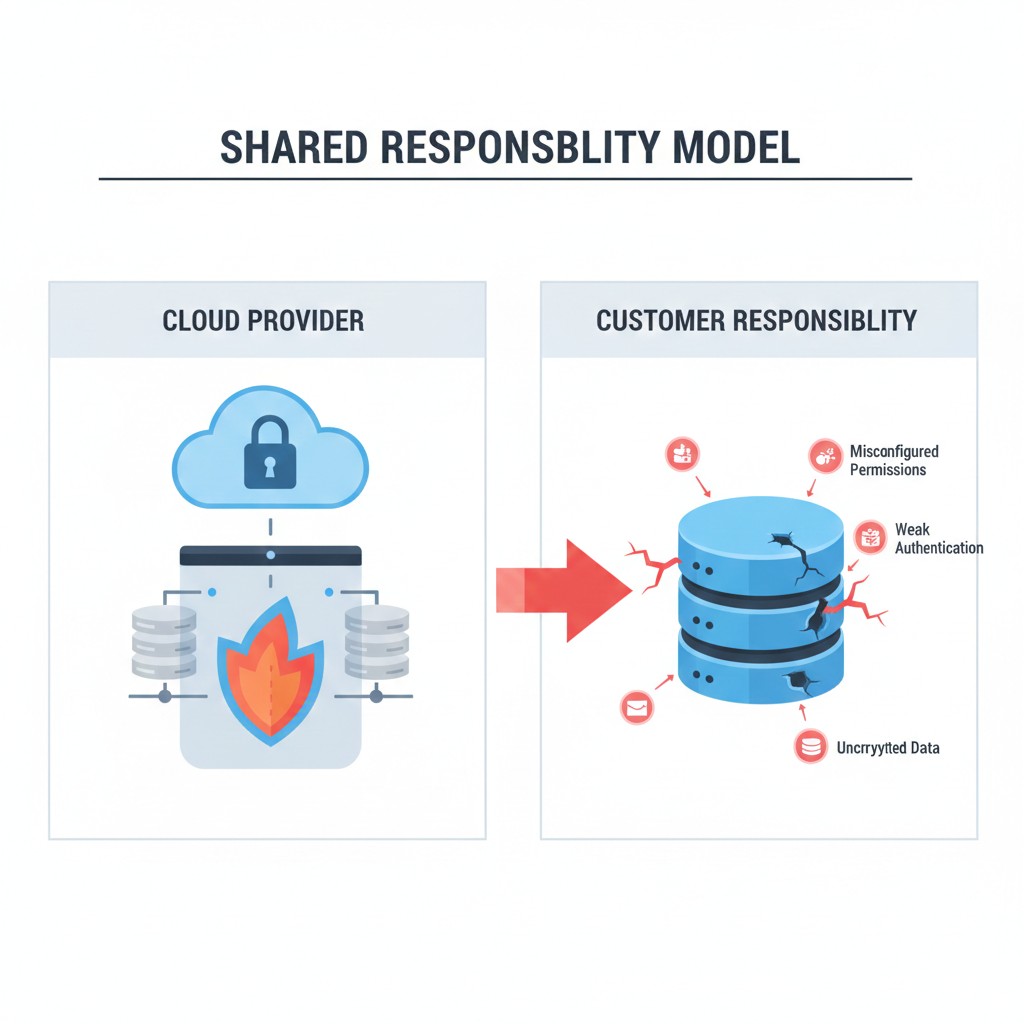
Shared Responsibility Misunderstood
In cloud environments, the shared responsibility model is often misunderstood. Cloud providers secure the infrastructure, but database security remains the customer’s responsibility. Misconfigured permissions, weak authentication, and unencrypted data are common causes of breaches.
Common Database Security Gaps in Enterprises
Excessive Privileges and Poor Access Control
One of the most common database security issues is excessive user privileges. Accounts are often granted broad access “just in case,” violating the principle of least privilege. Over time, this creates unnecessary risk, especially when credentials are reused or leaked.
Lack of Encryption and Key Management
Some organizations still fail to encrypt data at rest or in transit—or rely on weak key management practices. Without proper encryption, stolen database files or intercepted traffic can be easily exploited.
Strong database security includes robust encryption paired with secure, centralized key management.

The Role of Automation and Visibility
Limited Monitoring of Database Activity
Unlike network traffic, database activity often lacks sufficient monitoring. Without database activity monitoring (DAM), organizations struggle to detect:
- Suspicious queries
- Unusual access patterns
- Data exfiltration attempts
Database security without visibility is reactive at best.
Manual Processes Do Not Scale
As databases scale across cloud, hybrid, and multi-cloud environments, manual security processes break down. Automation is essential to enforce consistent policies, audit access, and respond to threats in real time.

Compliance Pressures Increase the Risk
Regulations Demand Stronger Database Security
Data protection regulations such as GDPR, HIPAA, and industry-specific standards place strict requirements on how data is stored, accessed, and audited. Weak database security makes compliance difficult and increases the risk of fines and legal exposure.
In many cases, organizations discover database security gaps only during audits or after incidents occur, as highlighted in recent cloud security incident lessons.
Audit Trails Are Often Incomplete
Without proper logging and audit trails at the database level, companies cannot prove compliance or investigate incidents effectively. Database security must include detailed, tamper-resistant logging to support governance and forensics.

Database Security in Modern Architectures
Cloud-Native and Distributed Databases
Modern applications rely on distributed and cloud-native databases that scale dynamically. While this improves performance, it also expands the attack surface. Database security strategies must adapt to:
- Dynamic workloads
- Ephemeral infrastructure
- Multiple database engines and services
Traditional security models struggle to keep up with this complexity.
DevOps Speed Creates New Risks
Rapid development cycles can unintentionally weaken database security. Schema changes, new services, and automated deployments may introduce vulnerabilities if security is not embedded into DevOps workflows.
Security must move at the same speed as development.
How Companies Can Close the Database Security Gap
To address database security blind spots, organizations should:
- Implement least-privilege access controls
- Encrypt data at rest and in transit with strong key management
- Deploy database activity monitoring and alerting
- Integrate database security into DevOps and automation pipelines
- Regularly audit configurations and access policies
Database security is not a one-time project—it is an ongoing discipline that evolves with data usage and architecture changes.
Final Thoughts
In 2026, data continues to be one of the most valuable—and vulnerable—assets businesses own. Yet database security often lags behind other security investments, creating a dangerous blind spot. As threats grow more sophisticated and data environments more complex, ignoring database security is no longer an option.
Companies that prioritize database security protect not only their data, but also their customers, reputation, and long-term resilience. The organizations that close this gap will be far better prepared for the security challenges ahead.
